Hacking 101: 30 Minutes a Day to Master Real-World Skills
Table of Contents
TL;DR
- 30-minute daily routine that keeps you on track.
- Free, open-source tools that make learning practical.
- Structured roadmap from networking basics to web exploits.
- Real-world skills that land bug-bounty dollars.
- Community resources that keep you motivated.
Why this matters
I still remember the first time I stared at a wall of command-line utilities and thought, “How am I supposed to learn all this?” That feeling is common among aspiring hackers, IT pros, and developers: the learning curve feels endless, the hours pile up, and the pressure to get results can be crushing. The truth? Mastering hacking doesn’t require a PhD or a full-time bootcamp. It requires a clear purpose, consistent practice, and the right tools. When you set a 30-minute daily goal, you avoid burnout, keep momentum, and make progress that adds up over months.
Key pain points we’re tackling
- Overwhelming learning curve: Start with bite-size steps.
- Time constraints: 30 minutes a day is doable even with a 9-to-5 job.
- Physical toll: Avoid late-night grind by structuring sessions.
- Networking fundamentals: Build a solid foundation before moving to web attacks.
- Tool frustration: Learn how to read documentation and use community scripts.
- Boredom after basics: Transition to advanced exploits and bug-bounty hunting.
- Automation gaps: Automate recon to save hours.
- Reverse engineering: Use Python and Frida for Android and binary analysis.
- Publishing challenges: Share findings via blogs or YouTube to build a brand.
Core concepts
The hacking journey is like learning to play an instrument. You first learn the notes (networks), then scales (scanners), and finally a full song (real-world attacks). Below are the essential building blocks:
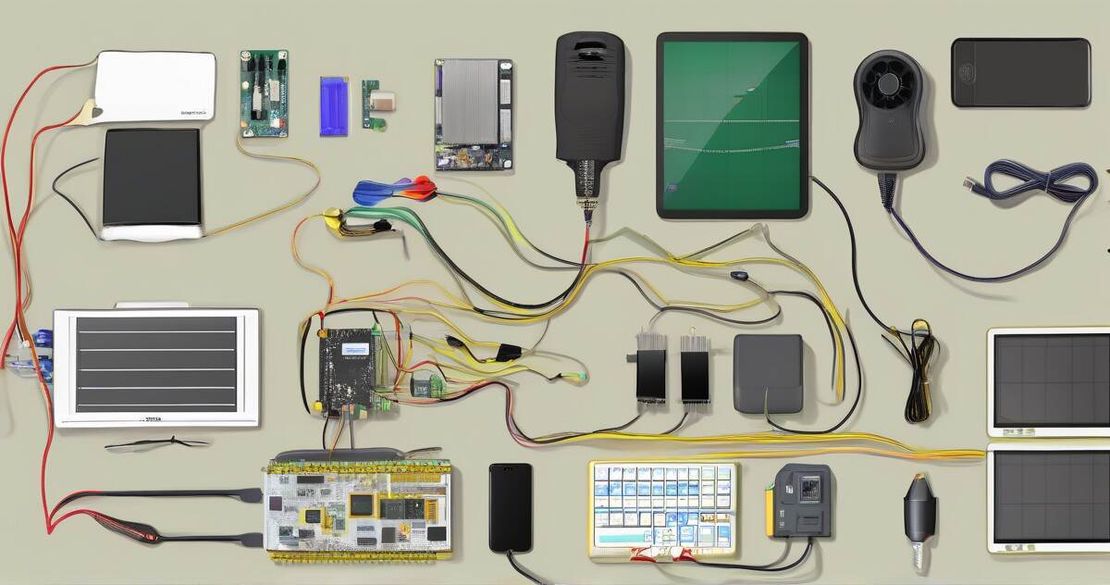
| Tool | What it does | Why you’ll use it |
|---|---|---|
| Kali Linux | A Debian-based distro packed with penetration-testing tools. | Kali Linux — Official Site (2024) |
| VirtualBox | A free hypervisor to run Kali safely on your laptop. | VirtualBox — Official Site (2024) |
| Nmap | Network scanner that discovers hosts, ports, and services. | Nmap — Official Site (2024) |
| Wireshark | Packet capture tool that visualises traffic. | Wireshark — Official Site (2024) |
| Metasploit | Exploitation framework with thousands of modules. | Metasploit — Rapid7 Help (2024) |
| Burp Suite | Web proxy that intercepts and manipulates HTTP traffic. | Burp Suite — PortSwigger (2024) |
| Port Swigger Academy | Interactive labs that walk you through XSS, CSRF, SQLi, and more. | Port Swigger Academy (2024) |
Networking fundamentals
- TCP three-way handshake: The handshake is how two devices agree to talk.
- IP addresses & ports: Think of an IP as a street address and a port as a mailbox.
- Protocols: Rules that decide how data is sent (e.g., HTTP for web pages).
Web vulnerabilities
- Cross-Site Scripting (XSS): Injection of malicious scripts that run in other users’ browsers. XSS — PortSwigger (2024)
- Cross-Site Request Forgery (CSRF): Tricks a user into sending a request they didn’t intend. CSRF — PortSwigger (2024)
- SQL Injection: Injecting SQL to read or modify databases. SQLi — PortSwigger (2024)
- Insecure Direct Object Reference (IDOR): Accessing objects you’re not allowed to. IDOR — Wikipedia (2024)
Mobile & reverse engineering
- Android Studio: Build and debug Android apps. Android Studio — Official (2024)
- Frida: Dynamic instrumentation for mobile apps. Frida — Docs (2024)
- Python: Write automation scripts that glue all tools together. Python — Docs (2024)
Community & career
- Cyberflow Academy: Private labs, mentors, and a community that keeps you accountable. Cyberflow Academy (2024)
- Bug bounty: Earn money by responsibly disclosing vulnerabilities.
How to apply it
Daily 30-minute routine
- 5 min – Review: Skim notes from yesterday.
- 5 min – Learn a concept: Watch a short tutorial or read a blog.
- 15 min – Hands-on: Apply the concept in a lab.
- 5 min – Reflect: Write a quick summary or tweet.
Monthly milestones
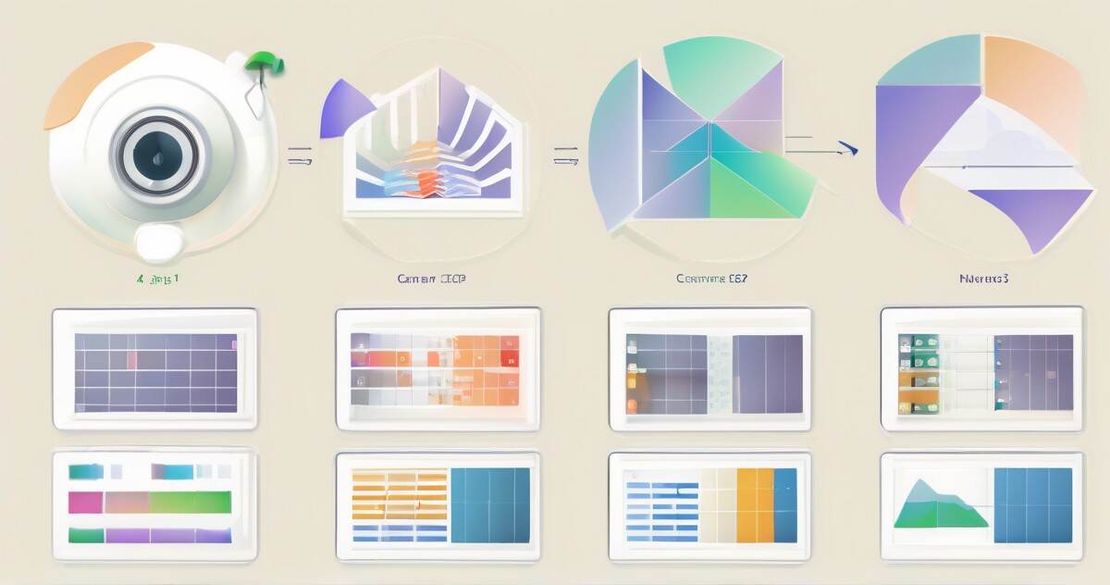
| Month | Goal | Tool(s) | What you’ll learn |
|---|---|---|---|
| 1 | Set up Kali in VirtualBox | Kali, VirtualBox | Virtualization basics, system hardening |
| 2 | Scan a local network with Nmap | Nmap | Host discovery, port scanning |
| 3 | Capture traffic with Wireshark | Wireshark | Packet structure, protocol analysis |
| 4 | Run a basic Metasploit module | Metasploit | Exploit delivery, session management |
| 5 | Finish a PortSwigger lab on XSS | Burp, PortSwigger Academy | XSS injection, mitigation |
| 6 | Run a basic bug-bounty program | Burp, Python scripts | Reporting, CVE tracking |
| 7+ | Deepen mobile testing | Android Studio, Frida | Reverse engineering, APK analysis |
Metrics to track progress
- 10 hours configuring the Android emulator (average).
- 90 % of people give up before week 12 – stay ahead by setting weekly wins.
- 3 years to first critical vulnerability on average – keep a log to see incremental gains.
Pitfalls & edge cases
- Burnout – If you feel exhausted after midnight, trim your sessions.
- Tool frustration – Metasploit’s module names can be cryptic; start with the manual.
- Boredom after basics – Once you can scan, start creating automated recon scripts in Python.
- Web vulnerability mix-ups – Keep a cheat sheet of payloads for XSS vs CSRF.
- Reverse engineering gaps – Use Frida tutorials to get comfortable with dynamic hooks.
- Publishing anxiety – Start small: write a note on a forum; gradually build a blog or YouTube channel.
- Lack of community – Join Cyberflow Academy or local meetups; feedback accelerates learning.
Quick FAQ
| Question | Answer |
|---|---|
| What is a TCP three-way handshake? | It’s the process where two devices agree on a connection: SYN → SYN-ACK → ACK. |
| How do I use Nmap for port scanning? | Run nmap -sS target for a stealth SYN scan. |
| What’s the difference between packet capture and network sniffing? | Packet capture collects raw packets; sniffing is the act of reading them. |
| How can I practice web vulnerabilities locally? | Spin up a Docker container of a vulnerable web app (e.g., OWASP Juice Shop) and use Burp. |
| How to set up an Android emulator for security testing? | Use Android Studio’s AVD Manager, install a recent system image, and install the app under test. |
| Why should I learn Python for hacking? | It’s lightweight, great for automating tools, and has libraries like Scapy for network tasks. |
Conclusion
You’re not alone on this journey. With a 30-minute daily window, the right tools, and a supportive community, you can transform from a curious hobbyist to a professional bug-hunter.
Actionable next steps
- Buy a laptop with at least 32 GB RAM (Reddit recommends this for smooth virtualization).
- Install VirtualBox and Kali Linux.
- Run your first Nmap scan and capture traffic in Wireshark.
- Complete a PortSwigger Academy XSS lab.
- Join Cyberflow Academy and set a weekly goal.
Who should use this guide
- Newcomers with no prior hacking experience.
- IT professionals looking to upskill.
- Developers wanting to secure their own projects.
Who should skip
- Those who cannot commit to any consistent learning schedule.
- Anyone looking for quick money without skill investment.
By following this roadmap, you’ll build the skills that make you valuable, the discipline to stay motivated, and the confidence to publish findings that pay.
References
- Kali Linux — Official Site (2024)
- VirtualBox — Official Site (2024)
- Nmap — Official Site (2024)
- Wireshark — Official Site (2024)
- Metasploit — Rapid7 Help (2024)
- Burp Suite — PortSwigger (2024)
- Port Swigger Academy (2024)
- XSS — PortSwigger (2024)
- CSRF — PortSwigger (2024)
- SQLi — PortSwigger (2024)
- IDOR — Wikipedia (2024)
- Android Studio — Official (2024)
- Frida — Docs (2024)
- Python — Docs (2024)
- Cyberflow Academy (2024)