I Tested a Credit Card in Acetone, Exposed a CIA Bug, and Traced 60 Years of Card Security
Table of Contents
TL;DR
- My acetone test proved credit cards survive extreme chemicals.
- The “Great Seal” bug showed that a passive listening device can be buried in plain sight.
- EMV’s 700-page standard replaced a single static magnetic stripe.
- UK and US contactless limits differ; UK has £100 per tap, US is unlimited.
- Chip-and-PIN adds ~10 s per transaction but cuts fraud by 76 % in the US and 63 % in the UK.
- Ghost-tapping requires you to be within ~4 cm; Faraday-cage wallets block it.
- Practical tips: keep cards in a Faraday pouch, enable instant-transaction alerts, and stay aware of contactless limits.
Why this matters
Every time you swipe, tap or scan a card, you’re handing over a tiny piece of technology that can be duplicated, hijacked, or eavesdropped on. Security researchers and everyday consumers alike often see cards as inert plastic, but the history of payment technology is a war against fraudsters who keep evolving new tactics. Understanding where the battlefield lies—magnetic stripe vs. chip vs. contactless—lets you choose the right tools and practices to keep your money safe.
Core concepts
| Technology | Core Feature | Typical Use | Main Security Risk |
|---|---|---|---|
| Magnetic stripe | Static encoded data | Swiping at a card reader | Cloning via magnetic dust |
| EMV chip & PIN | Dynamic cryptographic code | Inserting into a reader + PIN | Requires a physical touch, but is far harder to clone |
| NFC / Contactless | Radio-frequency communication | Tapping a card or phone | Short-range but can be intercepted if you’re too close |
Magnetic stripe – the original vulnerability
When credit cards first rolled out in 1970, the industry relied on a magnetic stripe that could be read with a simple magnet on a metal track. That design worked, but it also meant that anyone who could capture the stripe’s magnetic field could duplicate it in seconds – a process that became known as magnetic stripe cloning Magnetic stripe card — Wikipedia (1970).
EMV chip – the 700-page game changer
The EMV standard, published in 2002, set out a 700-page specification that required every card to carry a tiny chip that generates a one-time cryptographic code for each transaction. The result? A transaction that can’t be replayed or tampered with. The standard was designed by the same three firms that gave it its name – Europay, Mastercard, and Visa – and it now governs the majority of in-store payments worldwide The EMV Standard: Break, Fix, Verify (arXiv 2006.08249).
Contactless – speed vs. distance
The leap to contactless (NFC) added speed: a tap can finish in about 10 s, whereas a chip-and-PIN transaction takes roughly 20 s. That extra 10 s is not a trick of convenience; it’s the time the terminal spends waiting for a PIN, verifying it, and encrypting the data before sending it to the issuer. The speed advantage comes at a cost: because contactless works at very close range, it opens a new threat vector called ghost-tapping, where a thief can trigger a small, unnoticed transaction without the user’s consent. This attack requires the victim to be within roughly 4 cm of the device Near-field communication — Wikipedia (2026).
The Great Seal bug – a passive eavesdropper
In 1952, a tiny, battery-free listening device, later dubbed “The Thing”, was discovered hidden in a plaque on the U.S. Embassy in Moscow. It worked by resonating at a 900 MHz frequency and modulating that signal with sound from the surrounding environment. Because it had no power source, the device was invisible and could be switched on by shining a radio wave onto it. The fact that it operated from a plaque inside an embassy underscored how subtle the early days of surveillance could be The Thing (listening device) — Wikipedia (1945).
How to apply it
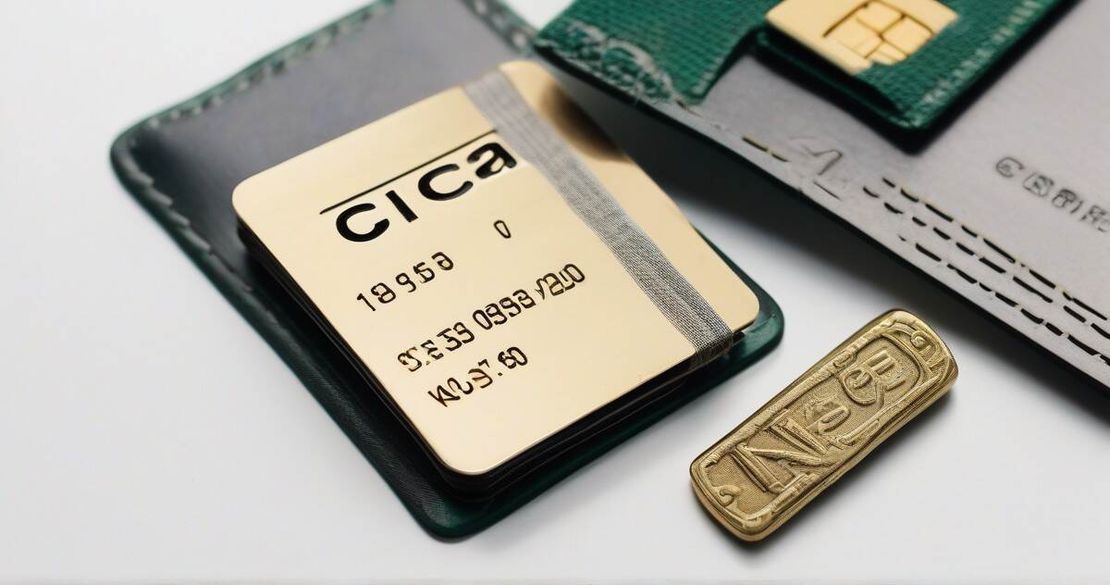
Choose the right card
- Stick with a chip-and-PIN card if you’re in the U.S. or the U.K. where the fraud reduction is proven.
- If you travel abroad, look for a contactless card that offers a high limit but also supports tokenized payments (Apple Pay, Google Pay) to keep your card data off the device.
Use a Faraday-cage wallet
- A pouch that blocks NFC signals (and all other RF waves) protects against ghost-tapping and RFID skimming. The SafeSleeve “Privacy Pouch” claims to block all Wi-Fi, Bluetooth, GPS, and NFC signals. It’s a simple, cheap, and effective tool. SafeSleeve Privacy Pouch — SafeSleeve (2026)
Enable instant-transaction alerts
- Banks and card issuers can now send a text or email whenever a transaction is authorized. The faster you notice an unauthorized charge, the faster you can freeze the card and prevent further loss.
Know your limits
- In the U.K., contactless is capped at £100 per tap, so if you need to spend more you’ll be prompted for a PIN. In the U.S., there is no statutory limit, but merchants can set one if they wish. A good practice is to keep a record of your daily contactless spend and set a personal budget that stays below the limit you’re comfortable with.
Keep your software up to date
- Many fraud schemes rely on old vulnerabilities. Updating your smartphone’s OS, your bank’s mobile app, and any payment-terminal firmware keeps you protected from known exploits.
Pitfalls & edge cases
| Issue | Why it matters | What to watch for |
|---|---|---|
| Magnetic stripe cloning | Still possible with old cards | Never rely on a magnetic stripe for high-value transactions |
| Ghost-tapping | Needs only ~4 cm proximity | Wear a Faraday pouch when you’re in crowded public spaces |
| Contactless limits | UK: £100; US: unlimited | Monitor your daily spend; set a personal threshold |
| Chip-and-PIN friction | Adds ~10 s per transaction | Trade off speed for security, especially in time-pressured environments |
| Real-time notifications lag | Some banks still batch alerts | Enable push notifications on your phone if possible |
Quick FAQ
| Question | Answer |
|---|---|
| What is magnetic stripe cloning? | It’s when a fraudster reads the magnetic data from a card and writes it onto a blank card. This creates a perfect copy that works for many merchants. |
| How does an EMV chip prevent cloning? | The chip creates a new cryptographic “one-time code” for every transaction, so a stolen code can’t be reused. |
| What is ghost-tapping and how close does it need to be? | A near-field communication attack that requires the attacker to be within about 4 cm of the card or phone. |
| How does a Faraday-cage wallet block NFC? | It’s a conductive enclosure that blocks electromagnetic fields, preventing the card’s radio from communicating with external readers. |
| Why does chip-and-PIN add extra seconds to checkout? | The terminal must wait for you to input a PIN, verify it, and generate a secure cryptographic code before sending the transaction to the issuer. |
| Do contactless limits differ between the UK and the US? | Yes – the UK caps contactless at £100 per tap; the US has no statutory limit, but merchants can set their own caps. |
| What should I do if my card is lost but still has a magnetic stripe? | Immediately report the loss, but also be aware that the stripe could still be cloned, so avoid using it for high-value transactions until you replace it with a chip card. |
Conclusion
The journey from the early magnetic stripe to today’s EMV chip and NFC has been a cat-and-mouse game. Every new layer of security has introduced a new attack vector, but it has also forced fraudsters to climb higher to stay ahead. By staying informed—knowing where the biggest risks lie, using a Faraday pouch, enabling instant alerts, and respecting contactless limits—you can keep your money out of the hands of thieves. As a security researcher, I’ve seen first-hand how a single acetone soak can prove a card’s resilience, and how a small, hidden bug on a Great Seal plaque can change an entire intelligence operation. That’s why the battle for payment security is far from over, and why it’s worth your time to arm yourself with knowledge.
Glossary
| Term | Definition |
|---|---|
| Magnetic stripe | A data strip of magnetically-coated material on a card that stores static information. |
| EMV | Europay, Mastercard, Visa – a global standard for chip-based payment cards. |
| NFC (Near-field communication) | Short-range radio-frequency communication used for contactless payments. |
| Faraday cage | A conductive enclosure that blocks external electric fields and radio waves. |
| Ghost-tapping | A contactless fraud technique that requires close proximity to trigger a transaction without the user’s consent. |
| Chip-and-PIN | A chip card that requires the user to enter a PIN to authenticate a transaction. |